A few months ago, Creighton’s Senior Director of Infrastructure and Operations mentioned an upcoming trip to Atlanta to meet with teams at Cisco and Georgia Tech. I didn’t have a lot of detail, or even a clear sense of what the return on investment might be for my role, but it felt like an opportunity worth exploring. In full disclosure, Creighton has recently begun standardizing on Cisco Room Bar systems in several conference rooms, so I already knew Cisco’s footprint extended well beyond the stereotypical view of “just a networking company.” Along with me, four other senior members of Creighton’s IT team made the trip.
Members of Cisco’s State, Local, and Education (SLED) team connected with us almost immediately once we arrived in Atlanta and invested a significant amount of time with us over the course of two days. Between shared meals and a full day spent at their Atlanta site, it was clear very quickly that this was more than a cursory briefing or sales stop. And their Atlanta space is something to see.

Cisco’s Atlanta Collaboration Center
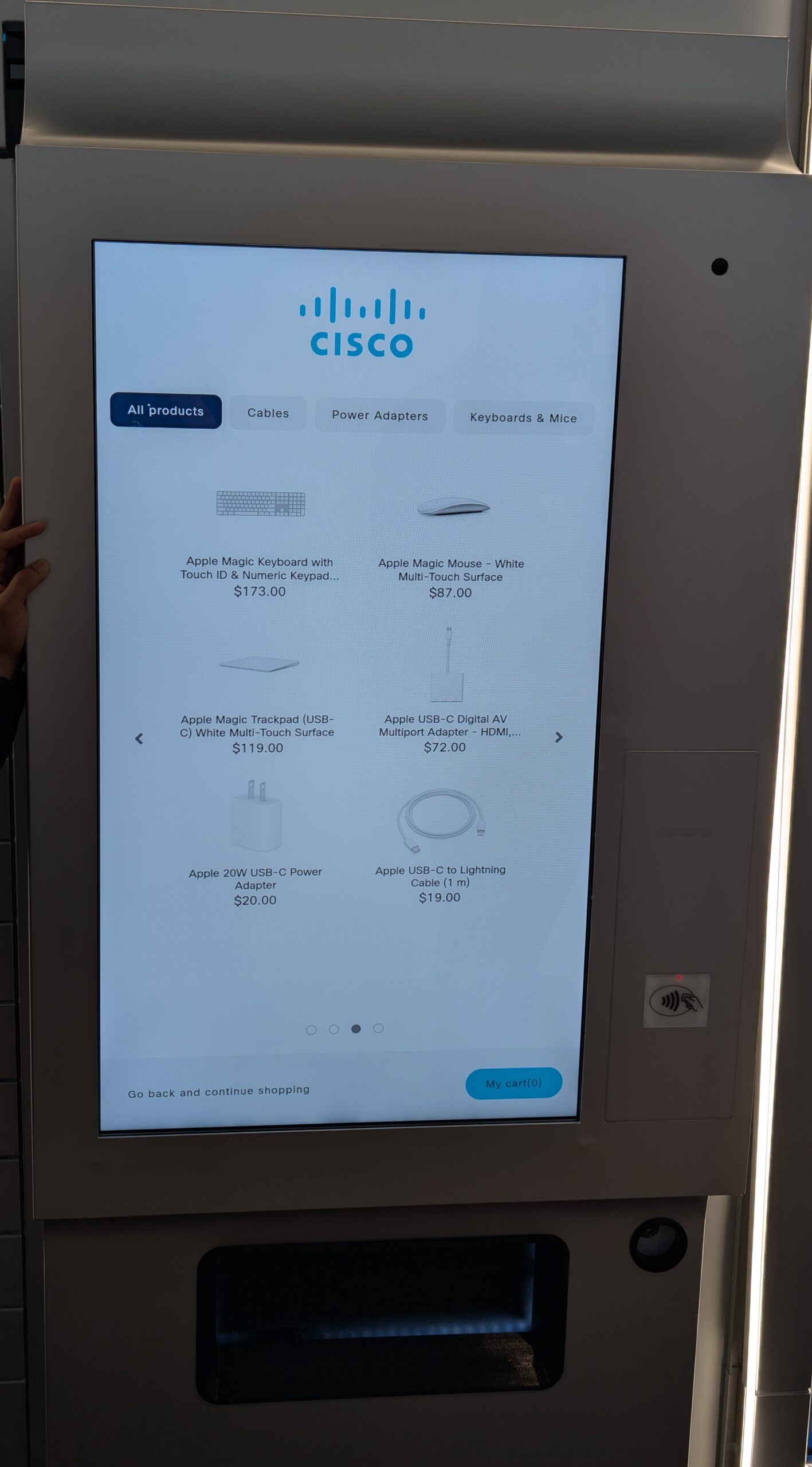
Visiting Cisco’s Atlanta Collaboration Center feels similar to walking a thoughtfully designed campus or touring a well-executed higher ed facility. Located on Georgia Tech’s campus, Cisco occupies five of the building’s 21 floors. That proximity is intentional. Students have access to the building and can engage directly with Cisco spaces, reinforcing the connection between industry, education, and real‑world application. The environment is organized around collaboration rather than individual workstation ownership, with a mix of spaces that support quick conversations, focused work, and larger group sessions.
From an AV standpoint, it is immediately clear that hybrid participation was treated as a baseline requirement, not an afterthought. Camera placement, audio coverage, and room layouts are designed so remote participants remain part of the experience rather than becoming a secondary audience on a screen. The result is a space where in‑person and remote collaboration feel intentionally balanced instead of awkwardly stitched together.
What stood out most from an AV and IT perspective is how deeply the building relies on data and network-based infrastructure. Lighting, environmental controls, sensors, and AV systems are all connected and feeding data back into the network, allowing the space to respond to real usage patterns instead of static assumptions. The building is not just “smart” in a marketing sense. It is constantly observing how spaces are used and adjusting accordingly.
That same data-driven approach has enabled a smaller overall footprint without the space feeling constrained. Large areas of underused desks have been replaced with flexible, purpose-built environments that support collaboration, focus, and movement. The result is a building that feels active and intentional, and it serves as a clear example of what can happen when AV, IT, and facilities are designed together instead of added on in sequence.
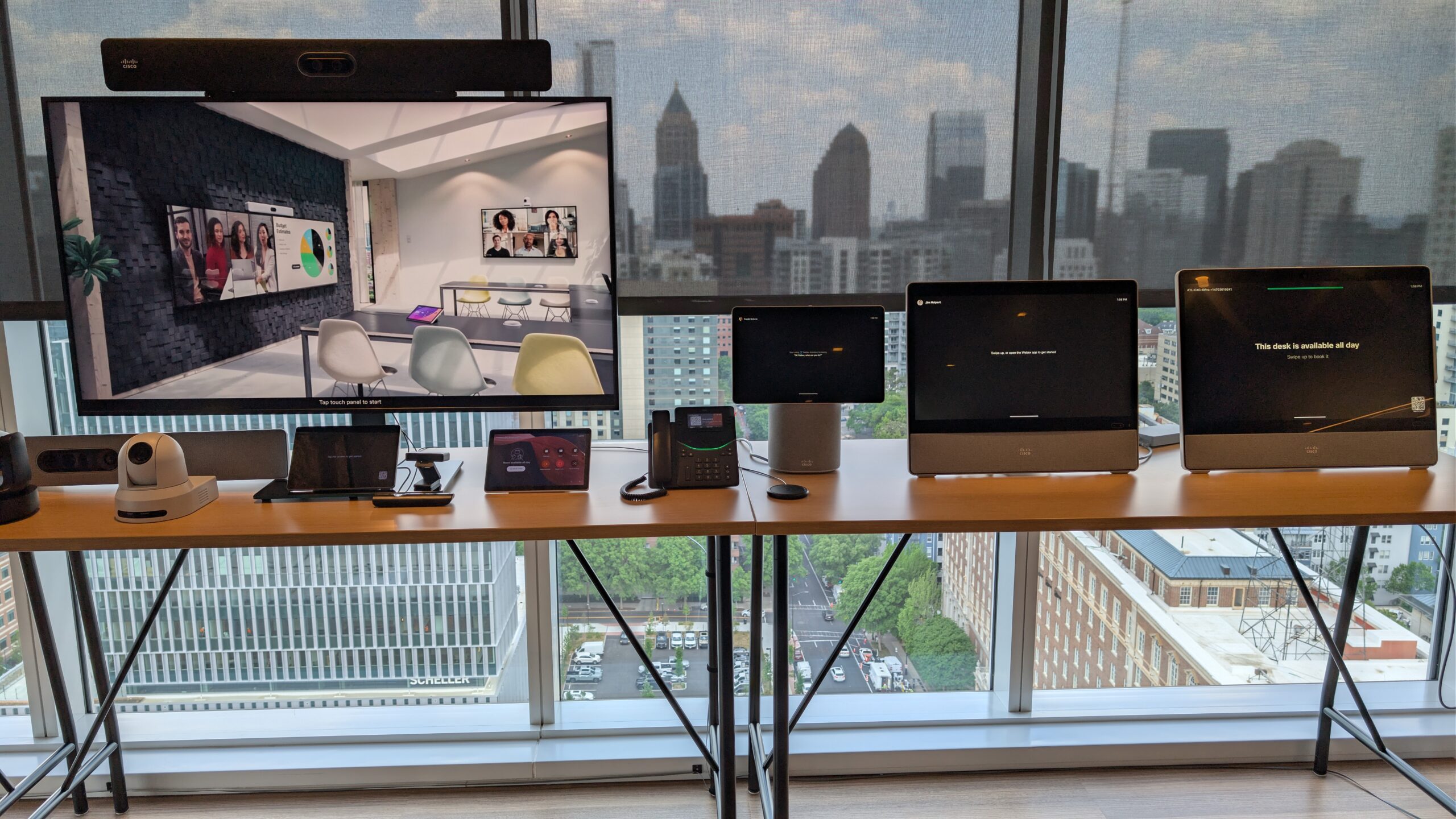
Technology is everywhere throughout the space, from more familiar cameras, ceiling microphones, and scheduling panels to conferencing bars and larger all‑in‑one collaboration systems with interactive whiteboards. Nearly everything is networked and feeding data back into the system, reinforcing how tightly AV is woven into the broader building infrastructure rather than standing alone as a separate layer.
One of the more eye‑opening moments for me was realizing how much capability already exists within tools we are actively deploying on campus. We have been installing Cisco Room Bars without fully appreciating that those same devices can support features like AI‑assisted active speaker identification, environmental sensing, and other data‑driven capabilities. As with other manufacturer collaboration spaces, there is real value in seeing this equipment used at scale, getting hands‑on time with it, and understanding how those features translate beyond spec sheets and into real spaces.
The space itself is also striking. It is filled with natural light, includes an accessible rooftop area, and feels genuinely welcoming, with meeting spaces spread throughout rather than clustered into formal zones. One standout feature is the world’s tallest freestanding spiral staircase, spanning all 21 floors. The photo I took doesn’t come close to capturing the scale. The rooftop offers impressive views of the Atlanta skyline and reinforces that this is a building meant to be experienced, not just occupied.

Session 1: Cisco in Higher Education
The first session framed Cisco’s higher education strategy around three primary focus areas: AI‑ready data centers, future‑proofed workplaces, and digital resilience. With roughly 80,000 employees globally, Cisco uses its own environments as living testbeds for an experience‑driven model built on four core pillars: ultra‑intelligent infrastructure, optimized hybrid operations, secure institutions, and reimagined interaction through applications.
What stood out was that this approach was not centered on enforcing presence or return‑to‑office mandates. Instead, the emphasis was on creating environments where people genuinely want to be. The physical campus is treated as an asset that must earn engagement, particularly in a hybrid world where people have real choices about how and where they work.
Session 2: Future-Proofed Workplace for Real Estate
This session zoomed out to show what happens when real estate, facilities, and IT are treated as a single system rather than parallel efforts. Cisco’s global workplace footprint spans hundreds of buildings across dozens of countries, supporting more than 136,000 connected stakeholders. That scale has pushed them toward consistent design standards and repeatable patterns that can be deployed, measured, and refined over time.
The workplace strategy centers on four pillars: user and operational experience, wellbeing, net‑zero goals, and data and insights. The unifying thread is that every system is designed not only to perform its function, but also to generate usable data. Buildings are treated as continuously measurable environments instead of static infrastructure that only changes during major renovations.
A key sustainability driver discussed in this session was the move toward low‑voltage, network‑powered systems. By removing traditional electrical cabling and delivering power over the network, devices such as lights, shades, sensors, and AV endpoints become first‑class network participants rather than standalone systems. This approach reduces AC‑to‑DC conversion losses, cuts embodied carbon from conduit and copper, lowers permitting and inspection overhead, and makes spaces far easier to adjust as needs change over time.
Just as importantly, this model creates meaningful visibility into how spaces are actually being used. Occupancy and traffic data can inform decisions around energy optimization, space planning, shuttle routing, parking availability, and ongoing maintenance. For AV and IT teams, the takeaway is that sustainability efforts and data strategy are no longer separate conversations. When everything is powered, connected, and observed through the network, environmental impact and operational insight come from the same design decisions.
Session 3: A/V Simplified
This session contrasted traditional classroom AV designs with an AV‑over‑IP approach, highlighting where complexity tends to build up over time. Conventional deployments often rely on HDMI transmitter‑receiver pairs to overcome distance limitations, along with plenum‑rated cabling, camera extension kits, third‑party DSPs, and ceiling microphones. Individually, each component solves a specific problem. Collectively, they increase cost, configuration time, and the number of potential failure points.
AV over IP was framed as a shift away from those workarounds. By moving audio, video, and control traffic onto the network, distance, power, and signal transport no longer drive system design decisions in the same way. Instead, rooms can be built around standard network infrastructure, aligning AV deployments more closely with how IT teams already design, deploy, and support technology.
Using Cisco’s AV‑over‑IP ecosystem as an example, the session showed how cameras, microphones, and room engines can connect directly over PoE, removing the need for HDMI extenders, dedicated DSPs, and localized power at endpoints. IP‑based PTZ cameras, table and ceiling microphones, and systems like the Room Kit Pro G2 consolidate what were previously separate subsystems into a smaller set of networked devices.
From an IT perspective, the impact is less about feature sets and more about operational simplicity. Rooms are easier to deploy, easier to support, and easier to troubleshoot because there are fewer devices in the signal chain and fewer specialized configurations to maintain. The takeaway was clear: AV over IP is not just a change in transport. It is an opportunity to align classroom and meeting‑space AV more closely with enterprise IT practices, reducing long‑term support burden while improving standardization and scalability.
Session 4: Security Landscape and Considerations for Higher Education
This session focused on why the traditional Security Operations Center model no longer aligns with how higher education institutions operate today. From roughly 2012 to 2019, most security strategies assumed on‑prem data centers, people working primarily on site, and clearly defined network perimeters to defend. That model made sense at the time, but it no longer reflects campus reality.
Today, data centers are distributed, work happens everywhere, and security must extend all the way to the endpoint. The presenter described the current security landscape as a patchwork of tools layered on over time, many of which are only touched a handful of times each year. When an incident does occur, that fragmentation makes it harder to quickly find the right data and respond effectively. The move to cloud services has only amplified this challenge, stretching teams thin and slowing response.
A central takeaway from the session was the need to simplify security operations while improving visibility and response speed. Cisco described consolidating security capabilities into three primary protection areas focused on users, cloud environments, and breach response, supported by threat intelligence from Talos. According to Talos, higher education is now the most targeted sector, adding urgency to the need for clarity and coordination rather than additional point solutions.
The proposed model emphasized a small set of core principles: AI‑enhanced detection, identity at the center of access decisions, and automation. Continuous authentication, adaptive risk‑based access, zero trust, and device posture assessment allow access controls to change in real time instead of relying on static, one‑time checks. Interoperability and automation were positioned as essential, using shared telemetry, response playbooks, and case management to reduce manual effort. Observing security events at massive scale reinforces a simple takeaway: modern security challenges are fundamentally problems of data, visibility, and response, not a lack of tools.
Session 5: End-to-End Secure Networking
This session framed Software Defined Networking as a response to operational complexity, not abstraction for its own sake. Traditional campus networks often depend on VLANs, subnets, and long access‑control lists that are tightly tied to physical location and topology. As devices move or spaces change, policies must be rewritten and revalidated, adding friction and increasing the chance of error.
SDN simplifies this model by clearly separating the control plane, data plane, and policy plane. Technologies such as LISP or EVPN manage control, VXLAN handles transport, and TrustSec defines policy, allowing intent to be expressed once and enforced consistently across the network. An intent‑based architecture translates business requirements into network behavior, validates that intent using telemetry, and continuously verifies that the network is doing what it was designed to do.
Segmentation and zero‑trust principles were presented as the real outcomes of this architectural shift. Rather than segmenting based on IP addresses or VLAN boundaries, devices and users are grouped by function using attributes such as identity, role, device type, location, and additional context pulled from systems like RADIUS and Active Directory. Endpoint Analytics leverages network telemetry and deep packet inspection, feeding that information into machine‑learning models to reduce unknown devices and improve classification over time.
Cisco ISE was positioned as the system that ties identity, context, and policy enforcement together, while pxGrid allows that shared context to extend across firewalls, cloud platforms, SD‑WAN, and secure service edge deployments. Enforcement moves closer to endpoints through smart switches and distributed security controls, reducing blast radius and improving resiliency. The end state is a policy model where access follows identity rather than topology, decisions adapt in real time, and segmentation becomes an ongoing lifecycle of classification, analytics, enforcement, and assurance instead of a one‑time configuration task.

Session 6: Preparing for Wi-Fi7 and 6 GHz
This shorter session focused on what the transition to 6 GHz and Wi‑Fi 7 actually looks like in campus environments. The headline feature of Wi‑Fi 7 is Multi‑Link Operation (MLO), which allows a client device to use multiple frequency bands at the same time rather than hopping between them. In practical terms, this supports lower latency, improved reliability, and smoother performance in busy spaces, particularly when 6 GHz is available as a relatively clean spectrum.
Moving traffic into the 6 GHz band also helps relieve congestion on 2.4 and 5 GHz, improving performance across the network as a whole. Importantly, the session emphasized that adopting Wi‑Fi 7 does not necessarily require a full redesign of access point placement. In many cases, existing AP locations remain viable, with the transition driven more by channel behavior, spectrum availability, and client capabilities than by starting over with a new RF design.
Security drove much of the discussion in this session. Operating in the 6 GHz band requires WPA3, which introduces stricter requirements than many campuses currently enforce. While transition modes allow WPA2 and WPA3 to coexist on 2.4 and 5 GHz, 6 GHz clients must use WPA3 with protected management frames enabled. Wi‑Fi 7 adds additional expectations around encryption and security behavior, including the use of stronger options such as GCMP‑256.
These requirements often force a rethink of SSID strategy, including separating open networks, enhanced open (OWE), and secured access. The key takeaway for AV and IT teams was that Wi‑Fi 7 adoption is far less about flipping a switch for speed and far more about aligning firmware versions, client readiness, and overall security posture. Supporting technologies such as BLE, fine time measurement, and ultra‑wideband were discussed as complementary tools, enabling faster beacon updates, improved ranging, and highly precise location services where needed, rather than as blanket solutions across the entire campus.
Conclusion
I arrived at Cisco unsure of what to expect and with a quiet assumption that much of the conversation might sit outside my day‑to‑day responsibilities. I left with a surprising number of actionable insights. Every member of the Creighton team came away with concrete follow‑ups, including additional conversations with Cisco and plans for a return visit in the not‑too‑distant future.
What stood out most was how well the Cisco team understood higher education. These were not abstract technology discussions. The people we met were clearly experienced in working with our vertical, familiar with the operational and support challenges we face, and already collaborating with institutions navigating similar transitions. As of this writing, I already have a follow‑up meeting scheduled to discuss additional capabilities within our existing Room Bar deployments.
I do want to close with a sincere thank‑you to the Cisco team for inviting us to Atlanta and investing so much time and energy into the experience. More than the conversations themselves, what resonated was the genuine interest they showed in understanding our environment, our constraints, and our goals. The sessions were clearly tailored to our needs, and each discussion felt grounded in real institutional challenges rather than generic messaging.
Cisco operates several collaboration centers like this around the world. If you have the opportunity to engage with one, I would strongly encourage you to do so. The value is not in seeing technology demos, but in stepping back, asking better questions, and gaining perspective on how AV, IT, facilities, and security can move forward together. You may, like I did, walk away with more clarity and direction than you expected.
This article reflects observations and conversations from a visit to Cisco’s Atlanta Collaboration Center. Impressions are based on what was witnessed and discussed during sessions and may not capture every detail of the presentations.